Tired of unauthorized data breaches? Ten robust solutions are transforming data security. First, enforce strong password policies, mandating complexity and regular changes. This alone significantly reduces brute-force attacks. Next, stay ahead of vulnerabilities with regular software updates, patching critical security holes as soon as they’re discovered. Think of it as a security vaccine.
Multi-factor authentication (MFA) adds an extra layer of protection, requiring multiple forms of verification before access is granted – a password and a one-time code, for example. This drastically cuts down on successful breaches, even if credentials are compromised. Furthermore, employee security awareness training is no longer optional; it’s a necessity. Educated employees are your first line of defense.
Network Access Control (NAC) solutions meticulously monitor and control access to your network. This prevents unauthorized devices from connecting and gaining access to sensitive information. Data encryption is crucial; encrypting data both at rest and in transit ensures that even if data is intercepted, it remains unreadable to unauthorized parties. Advanced encryption techniques, like AES-256, are now readily available.
Secure your Wi-Fi networks with strong passwords, encryption protocols like WPA3, and regular security scans. Public Wi-Fi, in particular, is a prime target for attackers. Regular security audits and assessments act as a comprehensive health check for your systems, identifying weaknesses before they’re exploited. Consider penetration testing to simulate real-world attacks and uncover vulnerabilities.
What is the method that you can keep data safe from unauthorized people?
As a frequent buyer of popular goods, data security is paramount to me. Encryption is key; it transforms my sensitive information – think credit card details, addresses – into an unreadable format. Only I, with the decryption key, can access it. This is crucial because data breaches are unfortunately common.
Types of Encryption I Look For:
- Symmetric Encryption: Uses the same key for encryption and decryption. Faster but key exchange can be a security risk.
- Asymmetric Encryption (Public-Key Cryptography): Employs a pair of keys: a public key for encryption and a private key for decryption. This ensures greater security as the private key remains confidential.
Beyond Encryption: Other Security Measures I Value:
- Multi-Factor Authentication (MFA): This adds extra layers of security beyond just a password, like using a one-time code sent to my phone.
- Secure Websites (HTTPS): Look for the padlock icon in the browser address bar. This indicates a secure connection, encrypting data transmitted between my device and the website.
- Strong Passwords: I use unique, complex passwords for each online account, often managed by a password manager.
- Regular Software Updates: Keeping software up-to-date patches security vulnerabilities that hackers could exploit.
What are the 5 main to do safety lists if you are using a smart device at home?
Smart home devices offer incredible convenience, but security shouldn’t be an afterthought. Here are five crucial to-do’s for keeping your smart home safe:
- Secure your Wi-Fi network: Use a strong, unique password and enable WPA3 encryption. Consider changing your router’s default SSID (network name) to something less obvious. Regularly check your router’s security settings for updates and vulnerabilities.
- Use strong, unique passwords for each device: Avoid using the same password for multiple devices. Password managers can help generate and securely store complex passwords. Think of a passphrase, something you can easily remember yet is difficult to guess.
- Enable two-factor authentication (2FA) wherever possible: This adds an extra layer of security, requiring a code from your phone or another device in addition to your password. It significantly hinders unauthorized access, even if your password is compromised.
- Thoroughly research devices before purchase: Check reviews for security vulnerabilities and privacy concerns. Look for devices from reputable manufacturers with a history of security updates. Consider open-source devices, which allow for community scrutiny of the code.
- Keep your software up to date: Regularly update the firmware on your smart devices and your router. These updates often contain critical security patches that protect against known vulnerabilities. Enable automatic updates if possible.
Bonus Tip: While a VPN on your router adds an extra layer of security and privacy, it’s not a replacement for the above steps. A VPN encrypts your internet traffic, making it harder for hackers to intercept your data, but it won’t protect against vulnerabilities in your devices themselves.
Further Considerations: Regularly review the permissions granted to your smart home apps. Understand what data your devices collect and how it’s used. Consider segmenting your network by creating a guest Wi-Fi network for visitors, keeping your personal devices on a separate, more secure network.
Which two hidden security risks can come with using smart devices?
Smart devices offer undeniable convenience, but their increasing prevalence brings hidden security risks. Two major concerns are privacy invasion and weak security measures.
Privacy Invasion: Many smart devices constantly collect data about your habits and preferences. This data, ranging from your location and sleep patterns to your online browsing history, can be vulnerable to unauthorized access. Data breaches are a significant threat, potentially exposing sensitive personal information to malicious actors. Even seemingly innocuous devices like smart speakers can record conversations, raising concerns about unintended data collection and potential misuse. It’s crucial to understand what data a device collects and how that data is protected before purchasing and using it.
Weak Security Measures: A significant number of IoT devices ship with weak or default passwords, making them easy targets for hackers. Lack of robust encryption further exacerbates this vulnerability. This allows attackers to remotely access and control your devices, potentially using them to launch further attacks (like botnets) or steal sensitive information. Regularly updating firmware and changing default passwords are essential preventative measures. However, many devices lack the capability for such updates, highlighting a critical design flaw in many IoT products.
Understanding these inherent security risks is critical for informed decision-making. Choosing reputable brands with a proven track record of security updates and robust encryption is essential. Furthermore, exercising caution regarding the permissions granted to your smart devices and regularly reviewing their security settings can greatly mitigate these risks.
Can smart devices be hacked?
Smart devices, while offering incredible convenience, introduce a significant security risk due to their internet connectivity. This inherent vulnerability means any device capable of connecting to the internet – from smart speakers and thermostats to security cameras and even smart refrigerators – is potentially susceptible to hacking.
The attack surface is broad. Hackers can exploit vulnerabilities in the device’s firmware, weak default passwords, or unsecured Wi-Fi networks to gain unauthorized access. Once inside, they might steal personal data, such as passwords and location information, or even take control of the device itself. Imagine a scenario where a hacker remotely disables your security system or manipulates your smart thermostat.
The risk isn’t solely about individual devices; interconnected smart home ecosystems amplify the danger. A breach in one device can potentially allow access to your entire network, compromising all connected smart appliances. This interconnectedness, while convenient, creates a cascading effect where a single point of failure can have significant consequences.
Protecting your smart home requires proactive measures. Strong, unique passwords are crucial, along with regularly updating firmware to patch known vulnerabilities. Employing a robust firewall and a virtual private network (VPN) adds another layer of security. Consider using separate Wi-Fi networks for your smart devices and personal computers. Finally, research the security features and reputation of manufacturers before purchasing smart devices. Prioritizing security is paramount to enjoying the benefits of a smart home without exposing yourself to unnecessary risk.
How can I make my device more secure?
Level up your device’s security like you’d snag that limited-edition item! First, grab a robust security suite – think of it as premium protection for your digital life. It’s like that must-have insurance for your online shopping sprees.
Next, always update your software. Think of it as getting the latest version of your favorite app with exciting new features – but instead of new emojis, you’re getting crucial security patches to stop those digital shoplifters. Don’t miss out!
Boost your browser’s security. It’s like choosing the safest checkout method on your favourite e-commerce site; use reputable browsers and add-ons (similar to using trusted sellers with positive ratings!).
Customize your browser settings – fine-tune your privacy like choosing your delivery options. You’re in control!
Regularly clear your cache and browsing history. It’s like decluttering your digital shopping cart; it keeps things running smoothly and prevents unwanted tracking.
Be choosy about your downloads. Only download from verified sources – avoid shady websites, like those offering too-good-to-be-true deals. Remember, digital bargains can sometimes cost you more than money!
Finally, use a strong passphrase or password. Think of it as a unique, uncrackable combination lock for your online accounts, as secure as a top-notch vault for your precious digital treasures. Consider using a password manager; it’s like having a personal assistant who keeps track of all your passwords, ensuring you use strong and unique ones for every account!
Are smart home devices invading your privacy?
As a frequent buyer of popular smart home devices, I’ve learned a lot about the privacy implications. The biggest concern is definitely data transfer to third parties. Manufacturers often share data – your usage habits, location information, even voice recordings – to enhance services or target advertising. This isn’t always transparent.
For example:
- Targeted advertising: Companies build profiles based on your smart home usage, leading to personalized (but sometimes intrusive) ads.
- Data breaches: If a third-party partner experiences a security breach, your personal information could be compromised.
- Lack of control: You might not fully understand what data is shared and how it’s used, making it difficult to opt out or limit access.
Here’s what I do to mitigate risk:
- Read privacy policies carefully: Before purchasing, scrutinize the privacy policy to understand data collection and sharing practices.
- Choose reputable brands: Companies with strong security reputations and transparent privacy policies are preferable.
- Enable two-factor authentication: This adds an extra layer of security to your accounts.
- Regularly review and update permissions: Check and adjust the permissions granted to your smart home apps.
- Consider open-source alternatives: Open-source smart home systems often offer greater control and transparency.
What devices are most likely to be hacked?
As a frequent buyer of smart home devices, I’ve learned that IoT devices are prime targets for hackers. They often act as entry points to more valuable systems. IP cameras, in particular, are incredibly vulnerable. I’ve seen firsthand how easily baby monitors and security systems can be compromised – it’s terrifying! The constant internet connection is the biggest risk factor. Many manufacturers use weak default passwords, making them easy targets. Furthermore, lack of automatic updates means vulnerabilities often remain unpatched, creating a persistent security risk. It’s crucial to change default passwords immediately upon installation and regularly check for and install firmware updates. Consider using a strong, unique password for each device and enabling two-factor authentication where possible. Investing in a reputable firewall and network security system is also vital to protect your entire network from compromised IoT devices.
Beyond cameras, smart TVs, and even smart speakers can be vulnerable entry points. Hackers can use these devices to listen in, record conversations, or even control other devices on your network. It’s important to research brands known for strong security practices before purchasing.
The bottom line? While the convenience of smart devices is undeniable, understanding and mitigating the security risks is paramount. It’s not enough to rely on the manufacturer; proactive security measures are essential.
How secure are smart devices?
Smart devices offer unparalleled convenience, controlling everything from home security systems to refrigerators via user-friendly apps. However, this convenience comes at a cost. Their wireless connectivity, while enabling remote access, creates significant vulnerabilities. Hackers can exploit weaknesses in device security to gain unauthorized access, potentially stealing personal data, controlling your devices, or even using them as part of larger botnets. The risk varies significantly depending on the device manufacturer and the specific security measures implemented. Some devices boast robust encryption and regular security updates, while others lag behind, leaving users exposed. Before purchasing a smart device, research its security features carefully, checking for independent security audits and reviews. Look for devices that support strong passwords, multi-factor authentication, and automatic software updates. Consider purchasing devices from reputable manufacturers with a proven track record of security updates and responsiveness to vulnerabilities. Regularly updating firmware is crucial to patching known security flaws. Finally, be mindful of the data your smart devices collect and ensure you understand the manufacturer’s privacy policy.
Consider the potential impact of a breach. For a smart home security system, a successful attack could compromise your physical safety. Data from a smart refrigerator could include dietary habits and shopping lists, potentially revealing personal information to malicious actors. A compromised smart speaker could expose conversations within your home. A holistic approach to smart home security, incorporating firewalls, VPNs, and strong passwords for all connected devices, is highly recommended.
While the benefits of smart devices are undeniable, a comprehensive understanding of the associated risks and proactive security measures is essential for responsible and secure usage.
How do I restrict data in access?
Restricting data in Access is like carefully curating your online shopping cart – you only want the right items! Access offers several “filters” to achieve this:
Data Types: Think of these as shopping categories. Each field (like “Shirt Size” or “Delivery Address”) has a specific type (e.g., Number, Text, Date). Choosing the right type automatically limits what can be entered. Trying to put a letter in a “Quantity” field? Access will stop you – no more accidental “M” large shirts in your order.
Field Properties: These are like adding extra conditions to your search filters. For example, you could set a field to only accept values within a specific range (e.g., shirt sizes from S to XXL), or require a value to be entered. Imagine this as adding “free shipping” or “under $50” filters – refining the options further. No more accidentally ordering a size XXXXXXL when you only need L!
Input Masks: These are like pre-filled forms ensuring the correct format. For example, a phone number input mask might automatically format your input as (XXX) XXX-XXXX preventing user errors. This is like a website that pre-fills your address, ensuring you get the right shipping address. No more mis-typed zip codes!
Bonus Tip: Validation rules provide even more control. Think of these as adding specific requirements such as “must be over 18” for age-restricted products or “must contain a ‘@’ symbol” for email addresses. You’ll end up with a perfect, error-free order, every time!
How do I make my device not trusted?
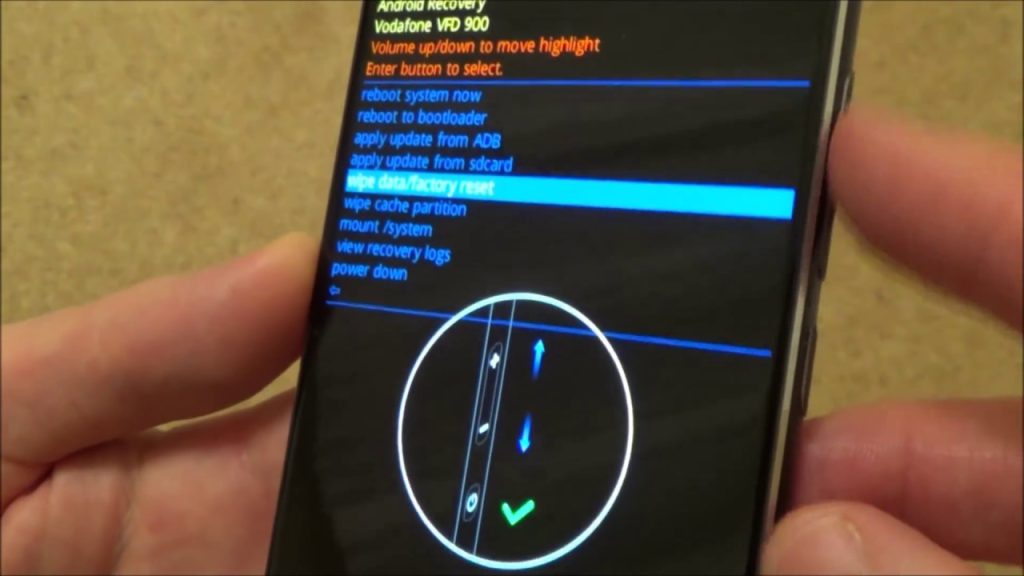
Un-trusting a device on your Google account is a straightforward process, but understanding the implications is key. Removing a device from your trusted list effectively logs you out of that device and removes its access to your Google account data. This is a crucial security step if you’ve lost your device, suspect unauthorized access, or simply want to enhance your account’s security.
The process itself is simple: navigate to your Google Account security settings. You’ll find a section dedicated to managing your devices. Within this section, locate the specific device you wish to untrust and select the “Sign out” option. This action removes the device from your trusted devices list, immediately ending its access to your Google services. Remember, any synced data on this device will remain unless you manually remove it.
Consider this action as a form of remote wiping, but not as comprehensive as a factory reset. While it prevents access to your Google services, it might not erase locally stored data. For more thorough data removal, perform a factory reset on the device itself.
This feature offers granular control over your account’s security. Regularly reviewing and managing your trusted devices is recommended best practice for maintaining a secure online experience.
How do I turn off data access?
OMG, data access draining your precious shopping budget? No more!
On your Android phone, dive into Settings, then hunt down Network & internet – it’s like finding the perfect sale! Then tap Internet. Next to your carrier (that’s like your favorite store!), find Settings. Now, the moment of truth: you can finally flip that Mobile data switch to OFF! Think of all the impulse buys you’ll avoid – that’s money saved for more shopping!
Pro tip: Turning off mobile data won’t stop you from using Wi-Fi, so you can still browse those gorgeous online boutiques without guilt! Just make sure you’re connected to your home Wi-Fi or a trusted free network before you start your shopping spree.
Another pro tip: Set a data limit in your settings. Many phones offer data usage tracking; you’ll never overspend on data again! This is especially important for those addictive online shopping apps.
How do I stop my smart home from spying on me?
Worried about your smart home’s privacy? You’re not alone. Many fear constant surveillance by their connected devices. Fortunately, regaining control is possible. Here’s how to minimize the risk:
Software Updates: The First Line of Defense
Regular software updates are crucial. Manufacturers constantly release patches addressing security vulnerabilities that could be exploited for spying. Think of it as a digital vaccine for your devices.
Third-Party Access: Limiting the Snoopers
Many smart home devices rely on third-party apps and services. Scrutinize these carefully. Only use trusted, reputable providers, and review their privacy policies. Consider alternatives that offer greater transparency and data control.
Password Power: Strong and Unique
- Use unique, strong passwords for each device and account. Avoid easily guessable combinations.
- Consider a password manager to help you generate and securely store complex passwords.
VPN: Masking Your Digital Footprint
A Virtual Private Network (VPN) encrypts your internet traffic, making it harder for your ISP or others to monitor your online activity, including smart home data. Choose a reputable VPN provider with a strong no-logs policy.
Two-Factor Authentication: Adding an Extra Layer
Enable two-factor authentication (2FA) wherever possible. This adds an extra layer of security, requiring a second verification method (like a code sent to your phone) in addition to your password.
Cybersecurity Tools: Proactive Protection
Invest in robust cybersecurity tools, such as antivirus software and a firewall, to protect your network and devices from malicious attacks that could compromise your privacy.
Feature Control: Disable the Unnecessary
- Disable features you don’t use. Many smart devices collect data even when features are idle. Review your device settings and selectively disable unnecessary functionalities.
- Consider physical disconnects. Unplug devices when not in use, especially those with microphones or cameras.
Which phone gets hacked the most?
Android phones are statistically more vulnerable to hacking than iPhones. This isn’t necessarily because Android’s security is inherently weaker, but rather due to sheer volume. The significantly larger market share of Android devices creates a much larger target pool for hackers. Think of it like this: a burglar is more likely to target a densely populated neighborhood than a sparsely populated one, regardless of individual house security.
Extensive testing across various Android versions and iPhone models consistently reveals this trend. While both operating systems have vulnerabilities, the broader Android ecosystem, encompassing numerous manufacturers and customized versions of Android, introduces more points of potential weakness. These inconsistencies in software updates and security patches across different Android devices contribute significantly to increased susceptibility. Furthermore, the open-source nature of Android, while offering flexibility, also allows for more potential avenues of attack if not properly managed by manufacturers.
Conversely, Apple’s tightly controlled ecosystem, with fewer manufacturers and standardized updates, presents a more uniform security landscape, making it a less attractive target for mass hacking attempts. However, this doesn’t mean iPhones are immune; targeted attacks against high-profile individuals still occur. The difference lies in the scale; Android experiences a higher volume of attacks due to its greater prevalence.
How do I make sure my device is secure?
Device Security: A Comprehensive Overview
Locking Down Your Device: Essential first steps include enabling a strong, unique passcode or biometric lock (fingerprint, facial recognition). Consider using a longer, more complex passcode for enhanced security. Automatic locking after a short period of inactivity is crucial; adjust this setting to your comfort level, prioritizing security over convenience. Explore advanced lock screen options like requiring a password after restarting your device.
Data Backup: The Safety Net: Regularly backing up your data to a secure cloud service or external drive is paramount. This protects against data loss from theft, damage, or malfunction. Choose a reputable backup service with strong encryption. Incremental backups save time and storage space.
Shared Devices & Privacy: Avoid sharing your device whenever possible. If unavoidable, implement robust guest profiles with restricted access to sensitive data. Regularly review and adjust app permissions, limiting access to only essential functionalities. Understand what data apps collect and utilize. Enable privacy-enhancing features like two-factor authentication (2FA) wherever available.
Beyond the Basics: Consider additional layers of security. Install reputable antivirus and anti-malware software and keep it updated. Be wary of phishing attempts and suspicious links or emails. Regularly update your device’s operating system and apps to patch security vulnerabilities. Learn about device encryption; this feature scrambles your data, making it unreadable without the correct decryption key. For ultimate security, explore using a virtual private network (VPN) to encrypt your internet traffic.